With the development of technology and science, biometric technologies are getting popular in most organizations and enterprises. Biometrics is becoming popular rapidly because it benefits people in so many ways. The technology offers numerous benefits or advantages in terms of security, economics, privacy, convenience, and accuracy.
Security, Privacy and Risk Management
Biometric technology is progressively increasing to add a layer of security to the use of smart cards. This technology is being deployed into application areas extending from access control to immigration. This technology provides the organization with a strong security advantage to eliminate any case of a card being borrowed, lost or stolen. It is also accomplishing a complete state of maturity, with its improved accuracy levels, reduced costs, and smaller template sizes. Biometric technology is not just limited to punch time in and time out, but smartphones and internet banking are making the most of this technology.
Use of Biometric technology in recognizing the identity and verify verifying the claimed identity. It works by measuring distinct physical characteristics or behavioral trade of an enrollee. Physical characteristics examples that are measured by biometric technology include the following.
Mazor Types of Biometric Technology
- Fingerprint
- Face
- Iris
- Hand geometry
Fingerprints Biometrics
Fingerprint biometric is one of the most mature biometric technologies. They are considered as a piece of legitimate evidence in courts of law all over the world. Fingerprints are used in forensic divisions worldwide for criminal investigations regularly. Fingerprint-based identification covers algorithms for fingerprint feature extraction, enhancement, matching, and classification.
The performance of these algorithms may be different depending on their use and technology. The mechanism of a fingerprint-based automatic identity authentication system consists of the following four components:
- User Interface
The user interface offers mechanisms for a user to show their identity and give input through fingerprints into the system.
- Enrollment module
The enrollment module functions to enroll persons and their fingerprints into the database of the system.
- System database
The system database comprises of a collection of records. Each of these records links to an authorized person who has accessibility to the system.
- Authentication module
The authentication module works to authenticate the identity of the person who aims to access the system.
Also read: What Is Pokemon Sleep? The Pokemon App Will Put You To Sleep!
Face Biometrics
Face is a very unique biometric among all because it is the only biometric which belong to both physiological and behavioral category.
Face recognition mainly involves the three tasks
- Verification: The recognition system finds if the claimed identity and stored face image match or not.
- Identification: The system figures out the identity of the query face image.
- Watch list: The recognition system first resolves if the identity of the query face image is on the watch list or not. If finds the face, it identifies the individual.
Framework for face pattern and face recognition approaches are classified according to their placements in their hierarchical framework. Further, methods for face recognition and modeling also entails age progression.
Biometric technology is constantly evolving and is being used in various sectors and organizations. At some level, the biometric system has become a vital part of the system. Mobile companies are integrating biometric security systems in smartphones and software development companies are deploying this technology into the apps to make it more secure and ensure the privacy of the users.
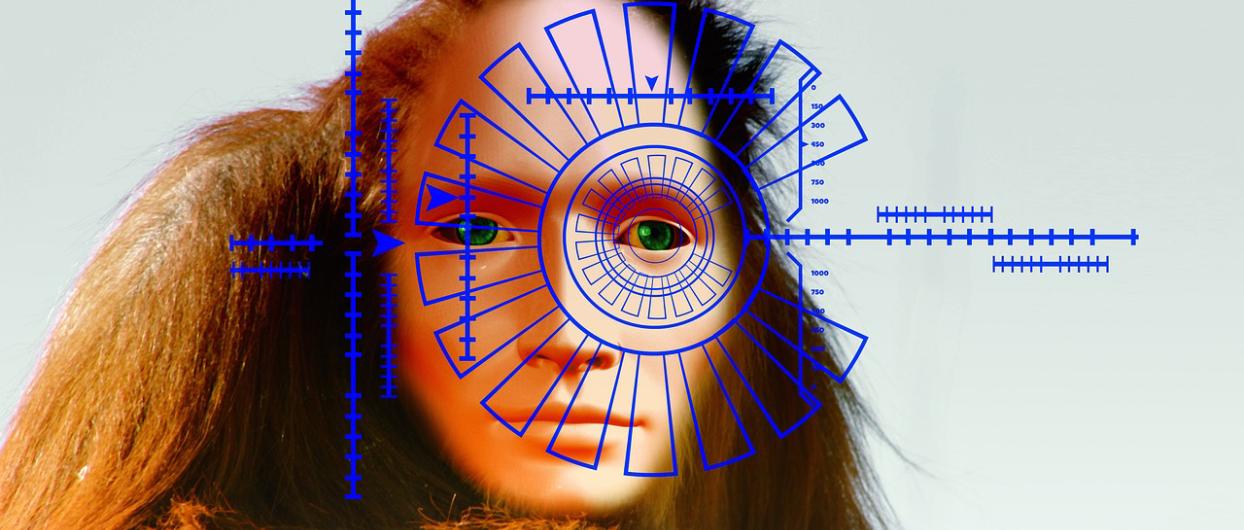
Iris recognition
The iris is the colored ring around the pupil of our eyes which controls its size and regulates the amount of light received. Like a thumbprint, Iris Recognition Iris Biometrics measures unique patterns in the colored circles of your eye to verify and validate your identity. Contactless, fast and renowned for its accuracy, biometric iris recognition can work over long distances, with some solutions requiring only a glance from a user.
Where can I get iris recognition?
Iris-based detection requires the use of specific hardware, as opposed to software-based modalities such as face and voice recognition, so it is less common in consumer deployments. But thanks to recent innovations in biometrics that have made the technology more accessible in terms of cost and installation, iris biometrics is becoming more prominent in vertical markets and in the consumer electronics sector.
How is iris identity making a difference?
Winthrop University has long been an example of iris biometrics in action with its EagleE presence tracking system.
Iris scanning plays an important role in the ongoing biometric border control pilot project along the US-Mexico land border.
Iris biometrics is used to protect CERN, a scientific facility in Geneva, Switzerland, famous for housing the large hadron collider.
Hand Geometry
Identification of a person Biometric methods based on the size of his hand. In its basic form, it is based on taking a picture of the user’s hand placed on the surface and after contour detection, finding and measuring singular points.
Advantages of hand geometry biometrics:
- Simple, relatively easy to use and inexpensive
- Environmental factors, eg, dry weather that causes skin to dry out is not a problem.
- Generally considered less intrusive than fingerprints, retina, etc.
Disadvantages of hand geometry biometrics:
- Hand geometry is not unique and cannot be used in detection systems
- Not ideal for growing children
Consider of use of biometric in a system
there are several factors included in the choice of biometric to use in a system. They are outlined in the paragraphs below.
Accuracy
Accuracy is one o the most vital cause one can go for availing of a biometric service. Iris technology is one of the most accurate and least error-prone to biometrics. This system requires a good view of the iris for fingerprint scanning. Some fingerprint technologies may not be strong for certain environments where dirt may be a cause of problems. Furthermore, errors may be connected to fingerprint damage or sometimes misreads off of a sensor. For instance, in the case of the sensor not cleaned, it could try to read two fingerprints together.
Ease of use
Fingerprint and face recognition systems are usually viewed as having the benefit of easiness and suitability. Unlike iris systems, face recognition technology only requires a glance at a system camera to get the needed information.
Budget
budget can be a serious consideration. An organization needs to carry the expenses of both establishing the system and on-going operation. Cost differences between biometrics depend chiefly on the location of system deployment. Cost differences are not always significant in a border control setting. This is probably because other infrastructure costs can be greater than the cost of biometric technology.
Public acceptability and cultural issues
The acceptance of technology by users is also important. However, people have become comfortable on the whole with the idea of fingerprint technology, there are still some lackings in the form of the fear of using it because of the associations of criminality. Sometimes, the use of iris recognition causes fear amongst citizens who have an incorrect belief that the process could impact their eyes.
Amount demands
Systems with a high demand of users need to be strong, less resilient, quick, and easy to use. Biometric technologies that are feasible for use in these areas may include iris, hand geometry and face recognition.
Top 10 News
-
01
Top 10 Deep Learning Multimodal Models & Their Uses
Tuesday August 12, 2025
-
02
10 Google AI Mode Facts That Every SEOs Should Know (And Wha...
Friday July 4, 2025
-
03
Top 10 visionOS 26 Features & Announcement (With Video)
Thursday June 12, 2025
-
04
Top 10 Veo 3 AI Video Generators in 2025 (Compared & Te...
Tuesday June 10, 2025
-
05
Top 10 AI GPUs That Can Increase Work Productivity By 30% (W...
Wednesday May 28, 2025
-
06
[10 BEST] AI Influencer Generator Apps Trending Right Now
Monday March 17, 2025
-
07
The 10 Best Companies Providing Electric Fencing For Busines...
Tuesday March 11, 2025
-
08
Top 10 Social Security Fairness Act Benefits In 2025
Wednesday March 5, 2025
-
09
Top 10 AI Infrastructure Companies In The World
Tuesday February 11, 2025
-
10
What Are Top 10 Blood Thinners To Minimize Heart Disease?
Wednesday January 22, 2025