Without machine learning, it is difficult to deploy robust cybersecurity solutions. Machine learning can be used in tandem if there isn’t a rich, thorough, and complete approach to the data.
Cybersecurity systems can use MI to recognize patterns and learn from them to detect repeated attacks and adapt to new behavior.
(adsbygoogle = window.adsbygoogle || []).push({});
It is a useful tool for cybersecurity teams to be more proactive in responding to threats and preventing them from happening again. By reducing time spent on mundane tasks, it can help businesses make strategic use of their resources.
Machine Learning in Cyber Security
Cyber Security analysts may use ML in a variety of areas to improve their security procedures. This makes it easier for them to quickly identify, prioritize, deal with, and resolve new threats.
Automating Tasks
Machine learning can be used in cyber security to speed up repetitive tasks such as malware detection, vulnerability analysis, triaging intelligence, and network log analysis.
Businesses can incorporate machine learning into their security workflow to speed up the response to risks and mitigate them at a pace that is faster than with manual human abilities.
Customers can automate repetitive tasks, which allows them to scale up or decrease without having to increase the number of employees, thus lowering costs.
AutoML is the term that describes machine learning being used to automate tasks. AutoML is when repetitive tasks in development are automated to aid analysts, data scientists, and developers to be more productive.
Also read: Top 3 Lessons I Learned from Growing a $100K+ Business
Classification and Threat Detection
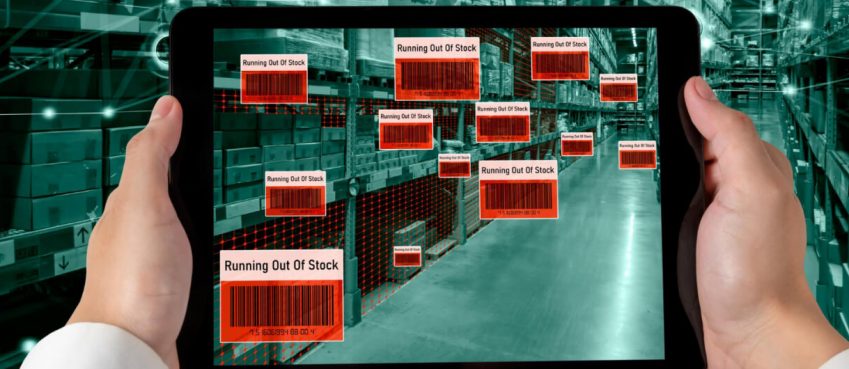
Machine learning is used in applications to detect and respond to threats. This can be achieved by analyzing large amounts of security events to identify harmful behavior patterns.
When similar occurrences are identified, ML uses the trained ML model to automatically deal with them.
You can create a database that will feed a machine-learning model by using Indicators of Compromise (IOCs). These data sets can be used to aid in real-time monitoring and identification of threats, as well as response. Malware activity can be classified by using ML classification algorithms or IOC data sets.
Darktrace, an Enterprise Immune Solution based on Machine Learning, claims to have stopped attacks during WannaCry’s ransomware epidemic.
Phishing
The traditional phishing detection algorithms can’t distinguish between malicious and innocent URLs. They aren’t fast enough nor accurate enough.
Machine learning algorithms are used to predict URL categories and detect suspicious patterns. The models are trained using characteristics such as email body data, punctuation patterns, and more to distinguish harmful emails from benign ones.
Also read: 14 Best Webinar Software Tools in 2021 (Ultimate Guide for Free)
WebShell
WebShell is a malicious software block that is installed on a website. It allows users to make modifications to the webroot folder of the server. Attackers have now gained access to the database. The bad actor can then access personal information.
Machine learning can recognize a regular shopping cart behavior and program the system to distinguish between malicious and normal behavior.
User Behaviour Analytics is a supplementary layer to standard security measures. It provides extensive visibility, detects account breaches, mitigates and detects malign or aberrant insider behavior, and provides comprehensive visibility.
Machine learning algorithms are used to classify user behavior patterns to identify natural behavior and detect suspicious activity.
Unexpected actions, such as late-night worker logins, unreliable remote access, excessive downloads, etc., are given a risk rating. This is based on user behavior, patterns, time, and other factors.
Also read: Best Video Editing Tips for Beginners in 2022
Network Risk Scoring
Quantitative methods to assign risk ratings to network segments help organizations prioritize resources. The ML can be used to analyze previous cyber-attack data and determine which regions are more often targeted by certain attacks.
This score can be used to assess the likelihood and impact of an attack on a particular network region. This makes organizations less likely to be the next targets of an attack.
You must identify which areas can compromise your company’s reputation when you do company profiling. This could be an accounting system, CRM, or sales system. It all comes down to identifying the areas that are most at risk.
Your firm might be rated low-risk if HR experiences a setback. Your entire industry could be affected if the oil trading system crashes. Each business is different in how they approach security. Once you understand the details of a company’s security, you will know which areas to protect. You’ll also know what priorities to take if there is a hack.
Human Interaction
As we all know computers excel at automating complex tasks and solving problems that are difficult for humans.
AI is mostly about computers but AI also requires people to make educated decisions and get orders. We might conclude that machines cannot replace people. Although machine learning algorithms can interpret spoken language and recognize faces, they still need people to do the job.
Also read: Everything You Need To Know About Drive4Walmart
Conclusion
Machine learning is an extremely powerful technology. It isn’t a miracle cure. It is important to remember that technology is constantly improving and machine learning and AI are moving at a rapid rate, but technology is only as strong as the brains and abilities of those who use it.
To exploit and identify flaws, malicious people will continue to improve their technology and skills. It is crucial to combine industry knowledge with the most advanced technology in order to quickly identify and respond to cyber threats.
Top 10 News
-
01
Top 10 Deep Learning Multimodal Models & Their Uses
Tuesday August 12, 2025
-
02
10 Google AI Mode Facts That Every SEOs Should Know (And Wha...
Friday July 4, 2025
-
03
Top 10 visionOS 26 Features & Announcement (With Video)
Thursday June 12, 2025
-
04
Top 10 Veo 3 AI Video Generators in 2025 (Compared & Te...
Tuesday June 10, 2025
-
05
Top 10 AI GPUs That Can Increase Work Productivity By 30% (W...
Wednesday May 28, 2025
-
06
[10 BEST] AI Influencer Generator Apps Trending Right Now
Monday March 17, 2025
-
07
The 10 Best Companies Providing Electric Fencing For Busines...
Tuesday March 11, 2025
-
08
Top 10 Social Security Fairness Act Benefits In 2025
Wednesday March 5, 2025
-
09
Top 10 AI Infrastructure Companies In The World
Tuesday February 11, 2025
-
10
What Are Top 10 Blood Thinners To Minimize Heart Disease?
Wednesday January 22, 2025